Generate Bitcoin Private Key From Words
Jul 23, 2017 Database Bitcoin Private Key 2017, bitcoin private key hack. Skip navigation Sign in. Bitcoin private Key and Address with balance generator 2018 - Duration: 1:56. Ratol astio 5,638 views. A seed phrase, seed recovery phrase or backup seed phrase is a list of words which store all the information needed to recover a Bitcoin wallet. Wallet software will typically generate a seed phrase and instruct the user to write it down on paper. If the user's computer breaks or their hard drive becomes corrupted. Use BitPay-style addresses for Bitcoin Cash (ie starting with 'C' instead of '1') Use legacy addresses for Bitcoin Cash (ie starting with '1') Encrypt private keys using BIP38 and this password: Enabling BIP38 means each key will take several minutes to generate.
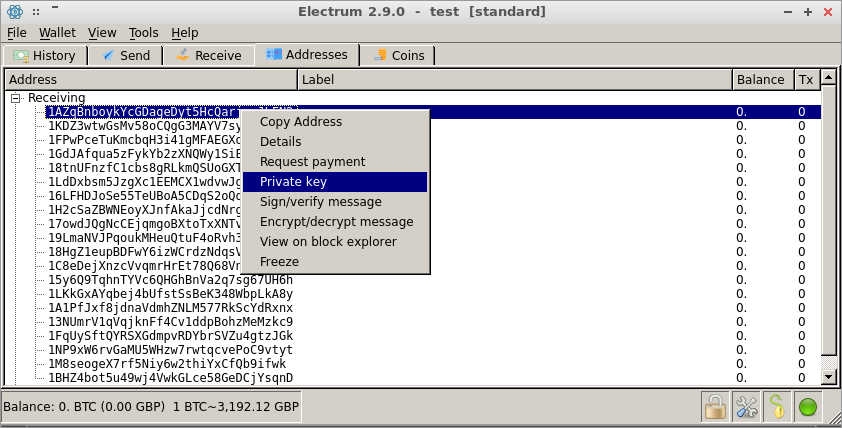
In cryptocurrencies, a private key allows a user to gain access to their wallet. The person who holds the private key fully controls the coins in that wallet. For this reason, you should keep it secret. And if you really want to generate the key yourself, it makes sense to generate it in a secure way.
Here, I will provide an introduction to private keys and show you how you can generate your own key using various cryptographic functions. I will provide a description of the algorithm and the code in Python.
Do I need to generate a private key?
Most of the time you don’t. For example, if you use a web wallet like Coinbase or Blockchain.info, they create and manage the private key for you. It’s the same for exchanges.
Mobile and desktop wallets usually also generate a private key for you, although they might have the option to create a wallet from your own private key.
So why generate it anyway? Here are the reasons that I have:
- You want to make sure that no one knows the key
- You just want to learn more about cryptography and random number generation (RNG)
What exactly is a private key?
Formally, a private key for Bitcoin (and many other cryptocurrencies) is a series of 32 bytes. Now, there are many ways to record these bytes. It can be a string of 256 ones and zeros (32 * 8 = 256) or 100 dice rolls. It can be a binary string, Base64 string, a WIF key, mnemonic phrase, or finally, a hex string. For our purposes, we will use a 64 character long hex string.
Why exactly 32 bytes? Great question! You see, to create a public key from a private one, Bitcoin uses the ECDSA, or Elliptic Curve Digital Signature Algorithm. More specifically, it uses one particular curve called secp256k1.
Now, this curve has an order of 256 bits, takes 256 bits as input, and outputs 256-bit integers. And 256 bits is exactly 32 bytes. So, to put it another way, we need 32 bytes of data to feed to this curve algorithm.
There is an additional requirement for the private key. Because we use ECDSA, the key should be positive and should be less than the order of the curve. The order of secp256k1 is FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEBAAEDCE6AF48A03BBFD25E8CD0364141, which is pretty big: almost any 32-byte number will be smaller than it.
Naive method
So, how do we generate a 32-byte integer? The first thing that comes to mind is to just use an RNG library in your language of choice. Python even provides a cute way of generating just enough bits:
Looks good, but actually, it’s not. You see, normal RNG libraries are not intended for cryptography, as they are not very secure. They generate numbers based on a seed, and by default, the seed is the current time. That way, if you know approximately when I generated the bits above, all you need to do is brute-force a few variants.
When you generate a private key, you want to be extremely secure. Remember, if anyone learns the private key, they can easily steal all the coins from the corresponding wallet, and you have no chance of ever getting them back.
So let’s try to do it more securely.
Cryptographically strong RNG
Along with a standard RNG method, programming languages usually provide a RNG specifically designed for cryptographic operations. This method is usually much more secure, because it draws entropy straight from the operating system. The result of such RNG is much harder to reproduce. You can’t do it by knowing the time of generation or having the seed, because there is no seed. Well, at least the user doesn’t enter a seed — rather, it’s created by the program.
In Python, cryptographically strong RNG is implemented in the secrets module. Let’s modify the code above to make the private key generation secure!
That is amazing. I bet you wouldn’t be able to reproduce this, even with access to my PC. But can we go deeper?
Specialized sites
There are sites that generate random numbers for you. We will consider just two here. One is random.org, a well-known general purpose random number generator. Another one is bitaddress.org, which is designed specifically for Bitcoin private key generation.
Can random.org help us generate a key? Definitely, as they have service for generating random bytes. But two problems arise here. Random.org claims to be a truly random generator, but can you trust it? Can you be sure that it is indeed random? Can you be sure that the owner doesn’t record all generation results, especially ones that look like private keys? The answer is up to you. Oh, and you can’t run it locally, which is an additional problem. This method is not 100% secure.
Now, bitaddress.org is a whole different story. It’s open source, so you can see what’s under its hood. It’s client-side, so you can download it and run it locally, even without an Internet connection.
So how does it work? It uses you — yes, you — as a source of entropy. It asks you to move your mouse or press random keys. You do it long enough to make it infeasible to reproduce the results.
Are you interested to see how bitaddress.org works? For educational purposes, we will look at its code and try to reproduce it in Python.
Quick note: bitaddress.org gives you the private key in a compressed WIF format, which is close to the WIF format that we discussed before. For our purposes, we will make the algorithm return a hex string so that we can use it later for a public key generation.
Bitaddress: the specifics
Bitaddress creates the entropy in two forms: by mouse movement and by key pressure. We’ll talk about both, but we’ll focus on the key presses, as it’s hard to implement mouse tracking in the Python lib. We’ll expect the end user to type buttons until we have enough entropy, and then we’ll generate a key.
Bitaddress does three things. It initializes byte array, trying to get as much entropy as possible from your computer, it fills the array with the user input, and then it generates a private key.
Bitaddress uses the 256-byte array to store entropy. This array is rewritten in cycles, so when the array is filled for the first time, the pointer goes to zero, and the process of filling starts again.
The program initiates an array with 256 bytes from window.crypto. Then, it writes a timestamp to get an additional 4 bytes of entropy. Finally, it gets such data as the size of the screen, your time zone, information about browser plugins, your locale, and more. That gives it another 6 bytes.
After the initialization, the program continually waits for user input to rewrite initial bytes. When the user moves the cursor, the program writes the position of the cursor. When the user presses buttons, the program writes the char code of the button pressed.
Finally, bitaddress uses accumulated entropy to generate a private key. It needs to generate 32 bytes. For this task, bitaddress uses an RNG algorithm called ARC4. The program initializes ARC4 with the current time and collected entropy, then gets bytes one by one 32 times.
This is all an oversimplification of how the program works, but I hope that you get the idea. You can check out the algorithm in full detail on Github.
Doing it yourself
For our purposes, we’ll build a simpler version of bitaddress. First, we won’t collect data about the user’s machine and location. Second, we will input entropy only via text, as it’s quite challenging to continually receive mouse position with a Python script (check PyAutoGUI if you want to do that).
That brings us to the formal specification of our generator library. First, it will initialize a byte array with cryptographic RNG, then it will fill the timestamp, and finally it will fill the user-created string. After the seed pool is filled, the library will let the developer create a key. Actually, they will be able to create as many private keys as they want, all secured by the collected entropy.
Initializing the pool
Here we put some bytes from cryptographic RNG and a timestamp. __seed_int and __seed_byte are two helper methods that insert the entropy into our pool array. Notice that we use secrets.
Seeding with input
Here we first put a timestamp and then the input string, character by character.

Generating the private key
This part might look hard, but it’s actually very simple.
First, we need to generate 32-byte number using our pool. Unfortunately, we can’t just create our own random object and use it only for the key generation. Instead, there is a shared object that is used by any code that is running in one script.
What does that mean for us? It means that at each moment, anywhere in the code, one simple random.seed(0) can destroy all our collected entropy. We don’t want that. Thankfully, Python provides getstate and setstate methods. So, to save our entropy each time we generate a key, we remember the state we stopped at and set it next time we want to make a key.
Second, we just make sure that our key is in range (1, CURVE_ORDER). This is a requirement for all ECDSA private keys. The CURVE_ORDER is the order of the secp256k1 curve, which is FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFEBAAEDCE6AF48A03BBFD25E8CD0364141.
Finally, for convenience, we convert to hex, and strip the ‘0x’ part.
In action
Let’s try to use the library. Actually, it’s really simple: you can generate a private key in three lines of code!
You can see it yourself. The key is random and totally valid. Moreover, each time you run this code, you get different results.
Conclusion
As you can see, there are a lot of ways to generate private keys. They differ in simplicity and security.
Generating a private key is only a first step. The next step is extracting a public key and a wallet address that you can use to receive payments. The process of generating a wallet differs for Bitcoin and Ethereum, and I plan to write two more articles on that topic.
If you want to play with the code, I published it to this Github repository.
I am making a course on cryptocurrencies here on freeCodeCamp News. The first part is a detailed description of the blockchain.
I also post random thoughts about crypto on Twitter, so you might want to check it out.
A seed phrase, seed recovery phrase or backup seed phrase is a list of words which store all the information needed to recover Bitcoin funds on-chain. Wallet software will typically generate a seed phrase and instruct the user to write it down on paper. If the user's computer breaks or their hard drive becomes corrupted, they can download the same wallet software again and use the paper backup to get their bitcoins back.
Anybody else who discovers the phrase can steal the bitcoins, so it must be kept safe like jewels or cash. For example, it must not be typed into any website.
Seed phrases are an excellent way of backing up and storing bitcoins and so they are used by almost all well-regarded wallets.[1]
Seed phrases can only backups funds on the block chain. They cannot store funds involved in Off-Chain Transactions such as Lightning Network or Blinded bearer certificates. Although these technologies are in their infancy as of 2019 so its possible in future seed phrases could be used to backup them.
- 4Storing Seed Phrases for the Long Term
Example
An example of a seed phrase is:
The word order is important.
Explanation
A simplified explanation of how seed phrases work is that the wallet software has a list of words taken from a dictionary, with each word assigned to a number. The seed phrase can be converted to a number which is used as the seed integer to a deterministic wallet that generates all the key pairs used in the wallet.
The English-language wordlist for the BIP39 standard has 2048 words, so if the phrase contained only 12 random words, the number of possible combinations would be 2048^12 = 2^132 and the phrase would have 132 bits of security. However, some of the data in a BIP39 phrase is not random,[2] so the actual security of a 12-word BIP39 seed phrase is only 128 bits. This is approximately the same strength as all Bitcoin private keys, so most experts consider it to be sufficiently secure.[3]
It is not safe to invent your own seed phrase because humans are bad at generating randomness. The best way is to allow the wallet software to generate a phrase which you write down.
As seed phrases use natural language words, they have excellent error correction. Words written in bad handwriting can often still be read. If one or two letters are missing or unreadable the word can often still be deduced. The word list that the seed phrase words are drawn from is carefully chosen so that the first four letters of each word are enough to uniquely identify it. This compares well with writing down a raw private key where a single letter being unreadable or incorrect can make the private key useless (depending on the serialization format).
Two-Factor Seed Phrases
Seed phrases, like all backups, can store any amount of bitcoins. It's a concerning idea to possibly have enough money to purchase the entire building just sitting on a sheet of paper without any protection. For this reason many wallets make it possible to encrypt a seed phrase with a password.
The password can be used to create a two-factor seed phrase where both 'something you have' plus 'something you know' is required to unlock the bitcoins.
This works by the wallet creating a seed phrase and asking the user for a password. Then both the seed phrase and extra word are required to recover the wallet. Electrum and some other wallets call the passphrase a 'seed extension', 'extension word' or '13th/25th word'. The BIP39 standard defines a way of passphrase-protecting a seed phrase. A similar scheme is also used in the Electrum standard. If a passphrase is not present, an empty string ' is used instead.
Warning: Forgetting this password will result in the bitcoin wallet and any contained money being lost. Do not overestimate your ability to remember passphrases especially when you may not use it very often.
Warning: The seed phrase password should not be confused with the password used to encrypt the wallet file on disk. This is probably why many wallets call it an extension word instead of a password.
Storing Seed Phrases for the Long Term
Most people write down phrases on paper but they can be stored in many other ways such as memorizing, engraving or stamping on metal, writing in the margins of a book, chiseling into a stone tablet or any other creative and inventive way.
In the past many people have accidentally lost bitcoins because of failed backups, mistyped letters, forgotten hard drives, or corrupted SSD devices. It's also important to protect the seed from accidental loss.
It could be a good idea to write some words of explanation on the same paper as the seed phrase. If storing for the long term you may forget what a phrase is how it should be treated. A sample explanation that can be adapted is:
These twelve words have control over BITCOINS. Keep this paper safe and secret, like cash or jewelry. The bitcoin information on this paper is encrypted with a passphrase. It is part of a multisignature wallet and was made by Electrum bitcoin wallet software on 1/1/2019.
Paper and Pencil Backup
Through bitter experience it has been found that one of the most practical storage mediums is pencil and paper. The private keys of a bitcoin wallet are encoded into random words from a dictionary which can be written down. If your hard drive crashes, you can find the paper with the seed phrase and restore the entire wallet. As seed phrases use natural language words, they have good error correction. Words written in bad handwriting can often still be read. If one or two letters are missing the word can often still be deduced. The word list that the seed phrase words are drawn from is carefully chosen so that the first four letters of each word are enough to uniquely identify it.
For storing on paper writing with pencil is much better than pen[4][5].Paper should be acid-free or archival paper, and stored in the dark avoiding extremes of heat and moisture[6][7][8].
Bitcoin Private Key Generator
Metal Backup
Seed phrases can also be stamped or engraved into metal which is significantly more durable than paper. Metal backups are recommended if the threat model involves fire, water, extremes of temperature or physical stress.
Methods that are not recommended
Some methods that are not recommended are: storing in a file on a computer (including online), or storing online. /onboard-secure-cryptographic-key-generation.html.
Some people get the idea to split up their phrases, like storing 6 words in one location and the other 6 words in another location. This is a bad idea and should not be done, because if one set of 6 words is discovered then it becomes far easier to bruteforce the rest of the phrase. Storing bitcoins in multiple locations like this should be done with multisignature wallets instead.
The Shamir Secret Sharing algorithm is sometimes promoted as a way to divide control of bitcoins, but in practice there are many pitfalls and tradeoffs that make it not worth it. See the main article: Shamir Secret Snakeoil
Another bad idea is to add random decoy words that are somehow meaningful to you, and later remove them to be left only with the 12 word phrase. The phrase words come from a known dictionary (see next section), so anybody can use that dictionary to weed out the decoy words.
It's possible but risky to memorize (Brainwallets) seed phrases. This should probably only be done in situations that really need it, such as crossing a hostile border where one expects to be searched.
Word Lists
Generally a seed phrase only works with the same wallet software that created it. If storing for a long period of time it's a good idea to write the name of the wallet too.
The BIP39 English word list has each word being uniquely identified by the first four letters, which can be useful when space to write them is scarce.
Alternative name 'Mnemonic Phrase'
Seed phrases are sometimes called 'mnemonic phrases' especially in older literature. This is a bad name because the word mnemonic implies that the phrase should be memorized. It is less misleading to call them seed phrases.
Bitcoin Private Key Formats
The power of backups
An especially interesting aspect in the power of paper backups is allowing your money to be two places at once. At the London Inside Bitcoin conference the keynote speaker showed 25 paper backups they were carrying -- all password-protected. With that one can carry $100,000 which can instantly be moved to a phone or transferred yet with total security. If it's stolen then there is no risk because it is backed up elsewhere. That is powerful.[9]
Bitcoin Private Key Generator
See Also
Generate Bitcoin Free
References
- ↑Bitcoin.org: Choose your wallet
- ↑BIP39: Generating the mnemonic
- ↑BIP32: Security
- ↑Pencil Does Not Fade
- ↑How do I maintain a paper notebook that can remain for years?
- ↑Essential facts about preservation of Paper
- ↑Writing in a notebook with pencil
- ↑CoPAR: Creating records that will last
- ↑https://www.reddit.com/r/Bitcoin/comments/2hmnru/poll_do_you_use_paper_wallets_why_why_not_what/